The first warning came not from researchers or from the Food and Drug Administration (FDA). It came from a hacker named Jay Radcliffe.
Radcliffe, who has diabetes, was curious to see if he could hack his implantable insulin pump. At the Black Hat USA security conference in 2011, he demonstrated that it wasn’t difficult to take control of an insulin pump and deliver a lethal dose to a patient.
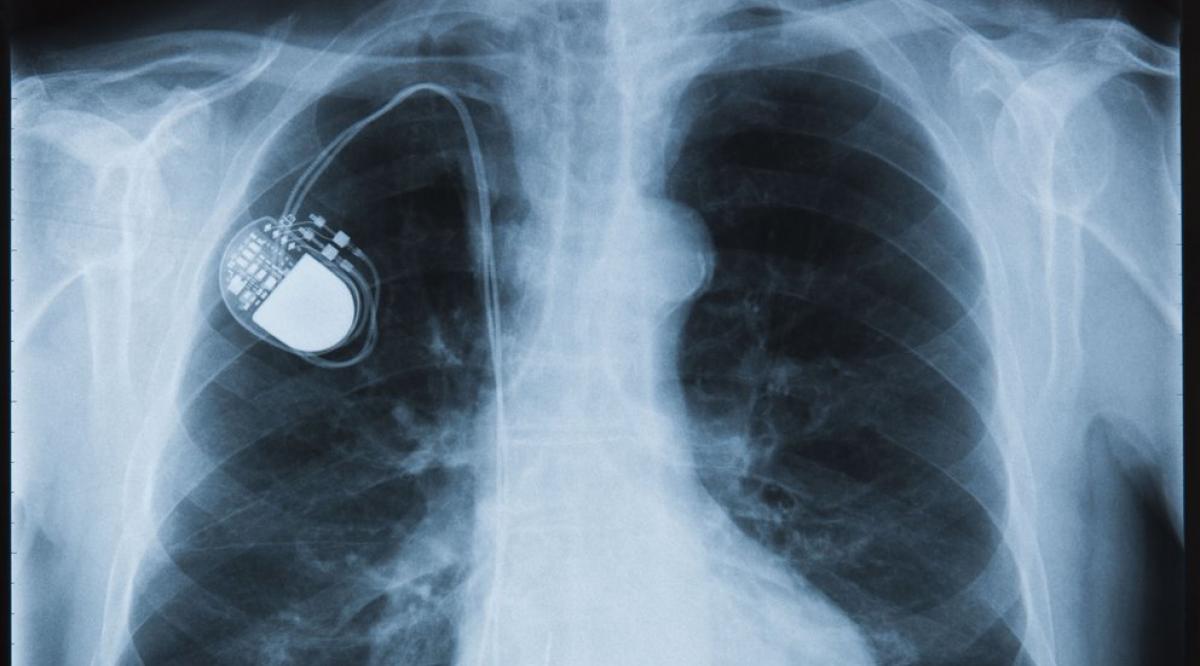
A year later, another hacker showed that pacemakers were also vulnerable to attack. Using a laptop, he demonstrated that it was possible to send a lethal electric shock to a patient via a pacemaker. A third hacker turned his attention to drug infusion pumps. They too could be tinkered with to administer dangerous or fatal doses of drugs to a patient.
In 2013, partly in response to these hackers’ revelations, the FDA issued its first guidance on cybersecurity and medical devices, and it has since issued several more advisories as concern over implantable or wearable medical devices intensifies. In 2017, for the first time, the FDA recalled an implantable pacemaker because of concerns that it could be hacked. And in October 2018, after hackers showed they could remotely manipulate another popular pacemaker, the manufacturer temporarily shut down part of its Internet network while working to secure the devices.
How serious is the risk? And what are leaders doing to keep patients and health care information systems safe from attack?
The network effect
When it comes to cybersecurity vulnerabilities in health care, implantable medical devices represent a relatively minor target for malicious hackers, most experts say.
“You can imagine a crazed science fiction novel where someone tries to kill someone by hacking a pacemaker,” says Dean Sittig, PhD, professor of biomedical informatics at the University of Texas Health Sciences Center at Houston. “But there’s not a lot of incentive for hackers to go after a target as small as a single pacemaker or infusion pump, unless that device is connected to a famous person like the leader of a country.”
“Doctors have to learn to recognize that these devices can malfunction or be disrupted and to treat that possibility as a differential diagnosis.”
Christian Dameff, MD
University of California, San Diego, Medical Center
But that’s no reason for complacency, says Jeff Tully, MD, an anesthesiology resident at the University of California (UC), Davis, Medical Center and part-time hacker who has led efforts to alert the medical community to the risks inherent in network-connected medical devices.
“Implantable devices live in an ecosystem of devices that are all connected,” Tully explains. “Any part of the network that is vulnerable to attack makes the network vulnerable.”
Indeed, implantable devices that are connected to the growing “internet of things” pose a particular risk, says Stephen Lopez, PhD, AAMC senior director of information security. “Implantable devices are often connected remotely, via wifi or radio frequency identification, in order to feed data back to a central information hub,” he explains. “If a patient’s home wifi is not secure, hackers could potentially get access to the central network through a wearable device.”
And once malicious hackers get into a health system, they may be able to grab electronic health records, release software viruses that could disrupt hospital operations, and launch a ransomware attack. In addition, even if the direct target isn’t an implantable medical device, malware introduced into a hospital IT system could spread to connected devices such as pacemakers or infusion pumps and disrupt their operations.
Tully, together with his colleague Christian Dameff, MD, a clinical informatics fellow at UC, San Diego, Medical Center, conducted a simulated attack to demonstrate just how vulnerable hospital networks can be if any portal — from an implantable device to a desktop computer — is compromised.
They showed how hackers could intercept blood and urine test results, alter them, and transmit the modified information into the electronic health record system. Those changes, they noted, could cause doctors to mistakenly prescribe incorrect, and potentially even deadly, treatments.
Bolstering cyberdefenses
Steps like upgrading operating systems and implementing security patches are key to helping prevent breaches, both for hospital-wide networks and personal devices connected to the networks, note experts.
In fact, hospitals and health care systems are devoting a growing proportion of their resources to preventing cyberattacks. According to a 2018 health information cybersecurity survey, more than 84% of responding organizations, which included hospitals and health care systems, increased resources to address cybersecurity concerns during the year. More than 83% had adopted new or improved security measures, and 65% replaced or upgraded IT software and related devices.
“It really comes down to patient safety. Addressing security risks is critical to the practice of medicine in the 21st century.”
Jeff Tully, MD
University of California, Davis, Medical Center
In addition, the Cybersecurity Act of 2015 established a Health Care Industry Cybersecurity Task Force to address a range of vulnerabilities in the health care industry. This year, the task force, a public-private collaboration that includes organizations from across health care, is expected to release new guidelines on medical device security as well as best practices guidelines for hospital IT experts.
But much more needs to be done, experts say. Protecting the security of implantable and wearable devices is particularly difficult because there are so many players, including manufacturers, hospital IT departments, health care providers, and patients. “Part of the challenge is that there isn’t a forum for hospitals and medical schools to address these complex issues in collaboration with device manufacturers and regulators, in order to establish best practices to prevent breaches,” says Lopez.
That’s changing. In 2018, the FDA issued a detailed new medical device safety plan, which includes a proposal to create a CyberMed Safety (Expert) Analysis Board, a public-private partnership that would serve as a resource for device makers, medical centers, and the FDA. The FDA also plans to implement greater premarket scrutiny of cybersecurity for medical devices and to improve its system for identifying and dealing with threats when they arise.
“In recent years, the FDA, manufacturers, and health care organizations have made significant progress to address and improve the cybersecurity of medical devices,” FDA Commissioner Scott Gottlieb, MD, said in a speech to the Medical Device Innovation Consortium 2018 annual forum. “But this is a rapidly evolving space. We know we all must keep pace.”
Doctors teaching doctors
As practicing physicians, Tully and Dameff are convinced that one crucial step is to educate health care providers that implantable and wearable devices can be hacked — and how to recognize and respond to an attack. In 2017, the two helped create the CyberMed Summit, an annual conference at the University of Arizona College of Medicine—Phoenix, where attendees have participated in simulations involving patients with compromised implantable devices. When something goes wrong, “often the last thing doctors consider is that a device has been hacked,” says Dameff. “Doctors have to learn to recognize that these devices can malfunction or be disrupted and to treat that possibility as a differential diagnosis."
Training in the basics of IT networks and networked devices should be part of standard medical school education, argue Dameff and Tully. They are collaborating with the Healthcare Sector Coordinating Council’s Cybersecurity Working Group to create a cybersecurity and IT technology curriculum that they hope medical schools will one day use. The curriculum will include training on how to interact safely with networked technologies and how to recognize when devices have been compromised.
“We can’t expect doctors to be IT experts,” says Tully. “But everybody who relies on these technologies needs to know the basics about what can happen if a hospital network is infected or a device is hacked.”
Ultimately, that effort will have to include training not only health care providers but patients and their families. “Preventing cyberattacks in health care is a socio-technical problem,” explains University of Texas informatics expert Sittig. “It requires manufacturers to design and maintain products that are secure. But it also depends on everyone using them to observe precautions like keeping passwords safe, not clicking on suspicious emails, and making sure home wifi systems are secured.”
Despite the recent recalls and warnings, most experts say, it’s essential to stress that the benefits of implantable devices like pacemakers and insulin pumps — and a host of similar devices being developed today — far outweigh any potential risks to patients.
“The challenge is how to design and maintain and use them to keep them safe as well as effective,” says Tully. “It really comes down to patient safety. Addressing security risks is critical to the practice of medicine in the 21st century.”